Archives: Projects
Projects

GRC Analyst Master Class
- Prepared, executed, and reported on audit of subset of NIST SP 800-53 cybersecurity controls to include interview, document review, and testing of systems to support compliance audit activities.
- Knowledgeable on NIST Cybersecurity Framework and how the Identify, Protect, Detect, Respond, and Recover categories comprise and facilitate an information security program
- Developed concise, tailored cybersecurity awareness content, improving targeted end-user base cyber hygiene
- Developed Just-In-Time cybersecurity awareness content for emerging threats to reduce operational risk to tailored audiences
- Semi-quantitatively analyzed cybersecurity risk using NIST SP 800-30 methodology to identify highest risk weaknesses for a system
- Executed threat modeling exercise to determine higher likelihood threat events to inform cybersecurity risk modeling

Virtualized 2012 R2 Windows Server Administration
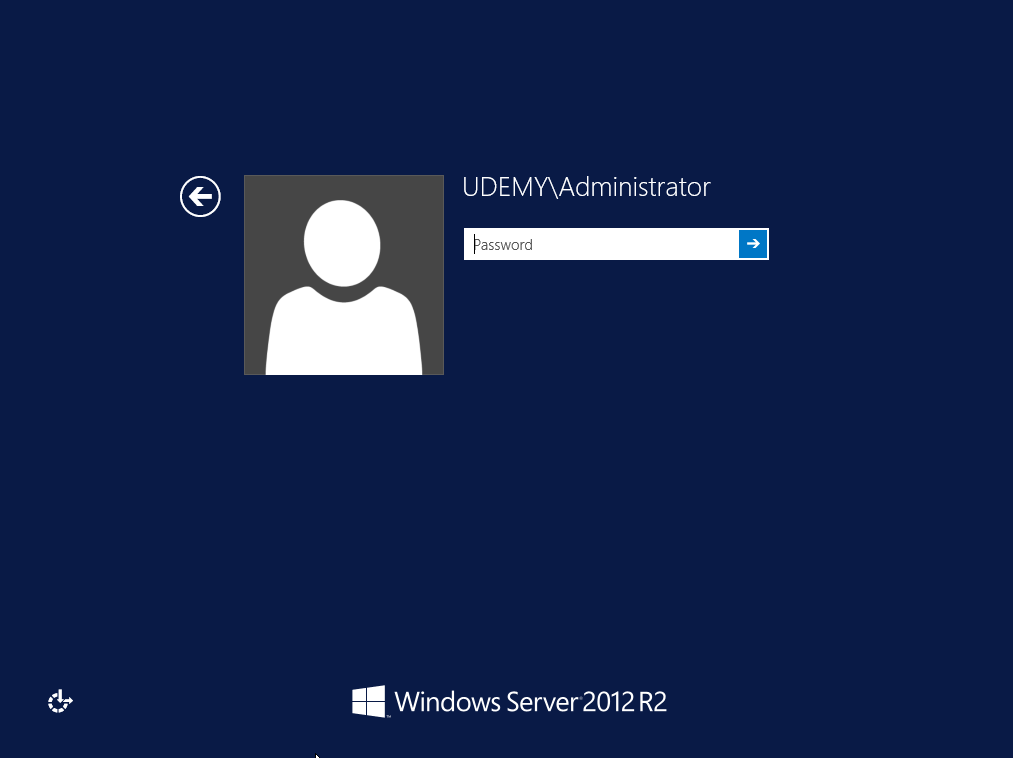
 Installed Virtual Box
Installed Win Server 2012 R2 VM
Installed Virtual Box
Installed Win Server 2012 R2 VM
 Added Active Directory services
Promoted to Domain Controller
Add configure 2nd drive
Create Windows Share/ Configure permissions
Added admin and User OU
Install 2 workstation VM"S for users
Added Active Directory services
Promoted to Domain Controller
Add configure 2nd drive
Create Windows Share/ Configure permissions
Added admin and User OU
Install 2 workstation VM"S for users
 Join VM's to Domain
Sign in as Domain User
Access Shares from domain user
Created Logon\Logoff script to log authenticated users
Join VM's to Domain
Sign in as Domain User
Access Shares from domain user
Created Logon\Logoff script to log authenticated users

ThreatGEN® Red vs. Blue Gamification
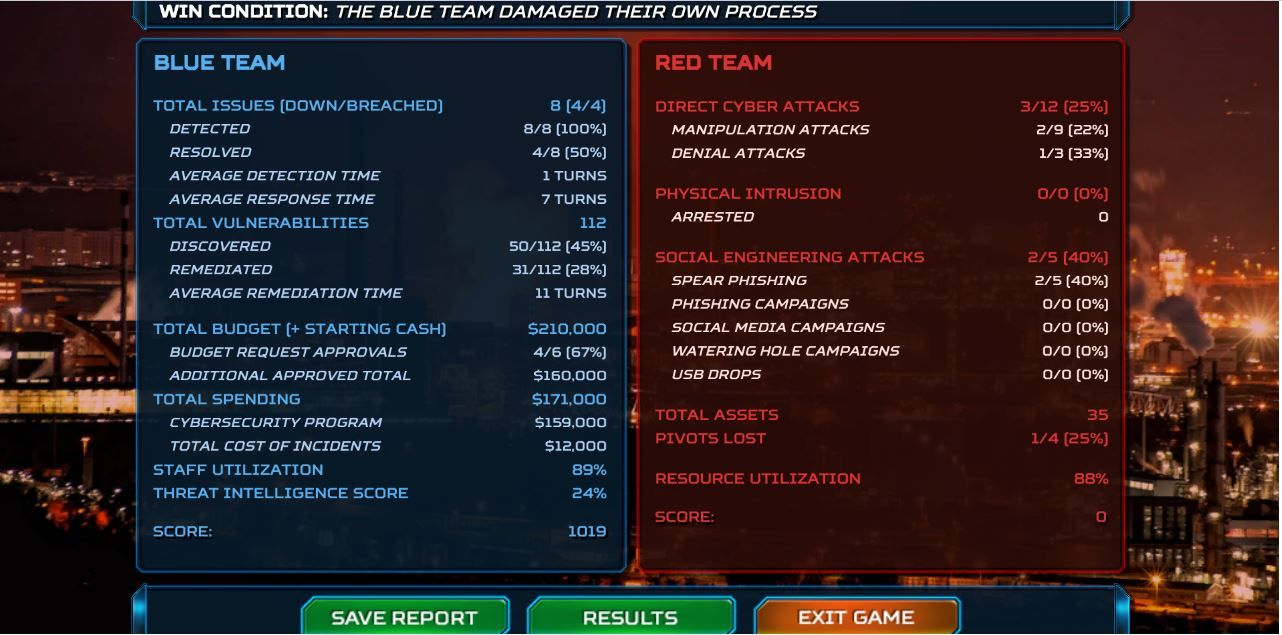
Blue Team 1 Red Team 0 Applying what I am using and learning through Gamification. ThreatGEN® Red vs. Blue is the next evolution in cybersecurity education, training, and IR tabletop exercises. It is a game-based cybersecurity simulation platform that combines the power of an actual computer gaming engine and active adversary simulation A.I., to provide the most practical and effective way for ANYONE to learn cybersecurity, from beginners to experts, and even leadership. It doesn't require any prior technical knowledge or command line skills... not even to play as the red team! Used for cybersecurity education, awareness, training, and IR tabletop exercises, ThreatGEN® Red vs. Blue is immersive, interactive, and hands-on, and it's supported by an education portal with online courses, labs, scenarios, and an online community.

nathandowd.tech website
Project URL: https://nathandowd.tech/projects/created-nathandowd-tech/
Signed up to Hostinger/Paid for domain and .tech extension Downloaded Network Chucks Theme and Plugin Set my Email domain Uploaded media(Certifications/Badges) Input text for fields Added an about me page linked to my who I am link Uploaded my resume for download Added a LinkedIn button Updated a typo in the MPCORE plugin(Miscellaneous , was causing navigation issues) Updated CSS Style

IT/Cyber Home Lab
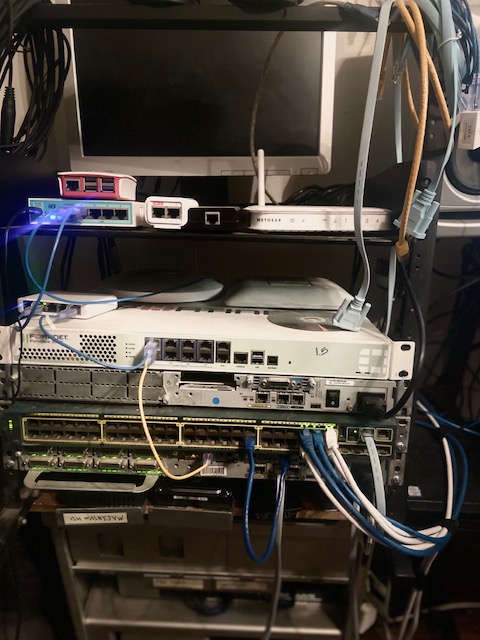
Project URL: https://nathandowd.tech/projects/it-cyber-home-lab/
I have created a home lab from networking equipment my previous employer was throwing away. I have created a mock small business network rack, A domain controller with users and groups. Administrators, Helpdesk and employees with access and permissions that adhere to principle of least privilege. A small network that's starts from my ISP's modem/router, I have it in bridge mode connecting to my Microtik router. My Mikrotik was set using unconventional ports for basic services like HTTP/HTTPS, FTP. It’s connected to a 5 port Unifi managed switch, I have my access points connected to it. I have 2 Vlans on that switch, the second Vlan is connected to a cisco router. I have turned my Mac pro into a VM workstation where I host most of them using Virtual Box. I have one in VM workstation. I have a vulnerable Vm that sits behind a PFsense firewall with no internet access to keep my hacking and practice secured. Network MikroTik Router Changed Admin Password Changed Default Ports Disabled unused services 5 Port managed switch Created Vlans 2 UAP’s(Broadcast open wifi to watch free network traffic, block certain activities, content filter, tried some wifi attacks) Cisco Switch (Vlans, Port Security) Cisco Router VM Workstation Virtual Box Windows DC (Win 10) AD Win 10 Helpdesk (Splunk(CCU)Nessus, Cisco Packet Tracer(CCNA) Win 10 User Ubuntu (LPI Linux Essentials training) CentOS (LPI Linux Essentials training) Kali Linux (NMAP, John The Ripper, Metasploit) Vulnerable Machine (Vuln Scan, patch and fix) Vmware Workstation ADHD-BHIS VM Fortigate Firewall (content filtering windows user)

AWS S3 Bucket Creation

Project URL: https://nathandowd.tech/projects/aws-s3-bucket-creation/
Created an AWS account Created S3 Bucket, name, location Blocked public access Set up our recordings to upload to our bucket

Ring Central VOIP Phone system

Project URL: https://nathandowd.tech/projects/ring-central-voip-phone-system/
Created auto receptionist call prompts Assigned Extensions Tested call queues, transferring, Caller ID, Callbacks, Call Monitoring, recorded calls Created and Registered user accounts Provisioned Polycom phones, Updated Speed dial Configured automatic call recording Created AWS S3 Bucket to save our call recordings

KnowBe4 Security Awareness Training
Project URL: https://nathandowd.tech/projects/knowbe4-security-awareness-training/
Sent out a test campaign to get a baseline, and decide what training could help us the most. Took that baseline and curated a program of different trainings to have our users go through.

Mail Guard 365 Implementation

Project URL: https://nathandowd.tech/projects/mail-guard-365-implementation/
Mailgaurd 365 sits on the inside of MS 365 and is the last check before emails make it to mailboxes. With Mailgaurd working in MS 365 this means it adheres to any policies, black or whitelisting we have in place already. This is our front line for stopping email threats, phishing schemes, and Ransomware attacks.

Alibi Camera System
Project URL: https://nathandowd.tech/projects/alibi-camera-system/
Implementing a new camera system at the three sites at work. Mapped locations where new cameras would be installed, and range of view the camera should have Replaced NVR's at all three sites Created user accounts and permissions w/least privilege